Logfile of HijackThis v1.99.1
Scan saved at 11:27:54 AM, on 08/23/2005
Platform: Windows 2000 SP4 (WinNT 5.00.2195)
MSIE: Internet Explorer v6.00 SP1 (6.00.2800.1106)
Running processes:
C:\WINNT\System32\smss.exe
C:\WINNT\system32\csrss.exe
C:\WINNT\system32\winlogon.exe
C:\WINNT\system32\services.exe
C:\WINNT\system32\lsass.exe
C:\WINNT\system32\svchost.exe
C:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
C:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
C:\WINNT\system32\spoolsv.exe
C:\Program Files\APC\APC PowerChute Personal Edition\mainserv.exe
C:\Program Files\ISS\BlackICE\blackd.exe
C:\PROGRA~1\NETSUP~1\client32.exe
C:\Program Files\Symantec AntiVirus\DefWatch.exe
C:\WINNT\SYSTEM32\DWRCS.EXE
C:\WINNT\system32\svchost.exe
C:\Program Files\ewido\security suite\ewidoctrl.exe
C:\Program Files\ewido\security suite\ewidoguard.exe
C:\Program Files\Novell\ZENworks\nalntsrv.exe
C:\Program Files\Novell\ZENworks\RemoteManagement\RMAgent\WolSerNT.exe
C:\Program Files\ISS\BlackICE\RapApp.exe
C:\Program Files\Novell\ZENworks\RemoteManagement\RMAgent\ZenRem32.exe
C:\WINNT\system32\regsvc.exe
C:\Program Files\Symantec AntiVirus\SavRoam.exe
C:\WINNT\system32\MSTask.exe
C:\Program Files\Analog Devices\SoundMAX\SMAgent.exe
C:\Program Files\Symantec AntiVirus\Rtvscan.exe
C:\Program Files\ISS\BlackICE\vpatch.exe
C:\WINNT\System32\WBEM\WinMgmt.exe
C:\Program Files\Novell\ZENworks\wm.exe
C:\PROGRA~1\PEREGR~1\DESKTO~1\bin\iftlsnr.exe
C:\Program Files\Novell\ZENworks\WMRUNDLL.EXE
C:\WINNT\system32\rundll32.exe
C:\WINNT\Explorer.EXE
C:\WINNT\SYSTEM32\DWRCST.exe
C:\WINNT\system32\NWTRAY.EXE
C:\Program Files\Microsoft AntiSpyware\gcasServ.exe
C:\Program Files\Common Files\Symantec Shared\ccApp.exe
C:\progra~1\symant~2\VPTray.exe
C:\Program Files\Microsoft AntiSpyware\gcasDtServ.exe
C:\Program Files\Novell\ZENworks\NALDESK.EXE
C:\Program Files\Microsoft Office\Office\1033\msoffice.exe
C:\Program Files\APC\APC PowerChute Personal Edition\apcsystray.exe
C:\WINNT\explorer.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
C:\Documents and Settings\RCORONEL\Desktop\HijackThis.exe
R0 - HKCU\Software\Microsoft\Internet Explorer\Main,Start Page = https://insidebny.ba...r/guestpage.htm
R3 - Default URLSearchHook is missing
O2 - BHO: (no name) - {53707962-6F74-2D53-2644-206D7942484F} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O3 - Toolbar: Yahoo! Toolbar - {EF99BD32-C1FB-11D2-892F-0090271D4F88} - C:\Program Files\Yahoo!\Companion\Installs\cpn1\yt.dll
O4 - HKLM\..\Run: [NWTRAY] NWTRAY.EXE
O4 - HKLM\..\Run: [Synchronization Manager] mobsync.exe /logon
O4 - HKLM\..\Run: [gcasServ] "C:\Program Files\Microsoft AntiSpyware\gcasServ.exe"
O4 - HKLM\..\Run: [ccApp] "C:\Program Files\Common Files\Symantec Shared\ccApp.exe"
O4 - HKLM\..\Run: [vptray] c:\progra~1\symant~2\VPTray.exe
O4 - HKLM\..\Run: [ZENRC Tray Icon] zentray.exe
O4 - HKLM\..\Run: [THGuard] "C:\Program Files\TrojanHunter 4.2\THGuard.exe"
O4 - Global Startup: APC UPS Status.lnk = C:\Program Files\APC\APC PowerChute Personal Edition\Display.exe
O4 - Global Startup: Application Explorer.lnk = C:\Program Files\Novell\ZENworks\NALDESK.EXE
O4 - Global Startup: Microsoft Office.lnk = C:\Program Files\Microsoft Office\Office\OSA9.EXE
O4 - Global Startup: Symantec AntiVirus.lnk = C:\Program Files\Symantec AntiVirus\VPC32.exe
O6 - HKCU\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O6 - HKCU\Software\Policies\Microsoft\Internet Explorer\Control Panel present
O6 - HKLM\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.5.0_04\bin\npjpi150_04.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.5.0_04\bin\npjpi150_04.dll
O9 - Extra button: Novell delivered applications - {C1994287-422F-47aa-8E5E-6323E210A125} - C:\Program Files\Novell\ZENworks\AxNalServer.dll
O10 - Unknown file in Winsock LSP: c:\program files\iss\blackice\ibe\icelsp_8.0.614.0.dll
O10 - Unknown file in Winsock LSP: c:\program files\iss\blackice\ibe\icelsp_8.0.614.0.dll
O10 - Unknown file in Winsock LSP: c:\program files\iss\blackice\ibe\icelsp_8.0.614.0.dll
O10 - Unknown file in Winsock LSP: c:\program files\iss\blackice\ibe\icelsp_8.0.614.0.dll
O12 - Plugin for .swf: C:\PROGRA~1\Netscape\COMMUN~1\Program\PLUGINS\NPSWF32.dll
O16 - DPF: Dialpad Webphone - https://www.dialpad....update/cham.cab
O16 - DPF: {62475759-9E84-458E-A1AB-5D2C442ADFDE} - http://a1540.g.akama...meInstaller.exe
O16 - DPF: {644E432F-49D3-41A1-8DD5-E099162EEEC5} (Symantec RuFSI Utility Class) - http://security.syma...n/bin/cabsa.cab
O16 - DPF: {74D05D43-3236-11D4-BDCD-00C04F9A3B61} (HouseCall Control) - http://a840.g.akamai...all/xscan53.cab
O16 - DPF: {917623D1-D8E5-11D2-BE8B-00104B06BDE3} (CamImage Class) - http://www.elunivers...sCamControl.ocx
O16 - DPF: {D2ACF167-BE52-11D1-92E0-0004ACB64296} - https://fa2.apollo.b...ExcelReport.CAB
O16 - DPF: {FE0BD779-44EE-4A4B-AA2E-743C63F2E5E6} (IWinAmpActiveX Class) - http://pdl.stream.ao.../ampx_en_dl.cab
O20 - Winlogon Notify: igfxcui - C:\WINNT\SYSTEM32\igfxsrvc.dll
O20 - Winlogon Notify: RunOnce - C:\WINNT\system32\vna64k.dll
O23 - Service: Peregrine Listener 6.0.1 (agtlsnr601) - Peregrine Systems, Inc. - C:\PROGRA~1\PEREGR~1\DESKTO~1\bin\iftlsnr.exe
O23 - Service: APC UPS Service - American Power Conversion Corporation - C:\Program Files\APC\APC PowerChute Personal Edition\mainserv.exe
O23 - Service: BlackICE - Internet Security Systems, Inc. - C:\Program Files\ISS\BlackICE\blackd.exe
O23 - Service: Symantec Event Manager (ccEvtMgr) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
O23 - Service: Symantec Password Validation (ccPwdSvc) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccPwdSvc.exe
O23 - Service: Symantec Settings Manager (ccSetMgr) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
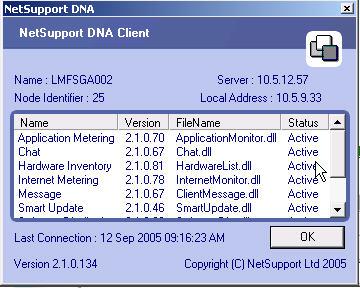
O23 - Service: Client32 - NetSupport Ltd - C:\PROGRA~1\NETSUP~1\client32.exe
O23 - Service: Client Update Service for Novell (cusrvc) - Novell, Inc. - C:\WINNT\system32\cusrvc.exe
O23 - Service: DB2 Security Server (DB2NTSECSERVER) - International Business Machines Corporation - C:\SQLLIB\bin\db2sec.exe
O23 - Service: Symantec AntiVirus Definition Watcher (DefWatch) - Symantec Corporation - C:\Program Files\Symantec AntiVirus\DefWatch.exe
O23 - Service: Logical Disk Manager Administrative Service (dmadmin) - VERITAS Software Corp. - C:\WINNT\System32\dmadmin.exe
O23 - Service: DameWare Mini Remote Control (DWMRCS) - DameWare Development LLC - C:\WINNT\SYSTEM32\DWRCS.EXE
O23 - Service: ewido security suite control - ewido networks - C:\Program Files\ewido\security suite\ewidoctrl.exe
O23 - Service: ewido security suite guard - ewido networks - C:\Program Files\ewido\security suite\ewidoguard.exe
O23 - Service: Novell Application Launcher (NALNTSERVICE) - Novell, Inc. - C:\Program Files\Novell\ZENworks\nalntsrv.exe
O23 - Service: Novell ZfD Wake on LAN Status Agent (Prometheus Wake-On-LAN Status Agent) - Novell Inc. - C:\Program Files\Novell\ZENworks\RemoteManagement\RMAgent\WolSerNT.exe
O23 - Service: RapApp - Internet Security Systems, Inc. - C:\Program Files\ISS\BlackICE\RapApp.exe
O23 - Service: Novell ZfD Remote Management (Remote Management Agent) - Novell Inc. - C:\Program Files\Novell\ZENworks\RemoteManagement\RMAgent\ZenRem32.exe
O23 - Service: SAVRoam (SavRoam) - symantec - C:\Program Files\Symantec AntiVirus\SavRoam.exe
O23 - Service: Symantec Network Drivers Service (SNDSrvc) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\SNDSrvc.exe
O23 - Service: SoundMAX Agent Service (SoundMAX Agent Service (default)) - Analog Devices, Inc. - C:\Program Files\Analog Devices\SoundMAX\SMAgent.exe
O23 - Service: Symantec AntiVirus - Symantec Corporation - C:\Program Files\Symantec AntiVirus\Rtvscan.exe
O23 - Service: ISS Buffer Overflow Exploit Prevention (VPatch) - Internet Security Systems, Inc. - C:\Program Files\ISS\BlackICE\vpatch.exe
O23 - Service: Workstation Manager (ZFDWM) - Novell, INC. - C:\Program Files\Novell\ZENworks\wm.exe

 This topic is locked
This topic is locked













 Sign In
Sign In Create Account
Create Account

