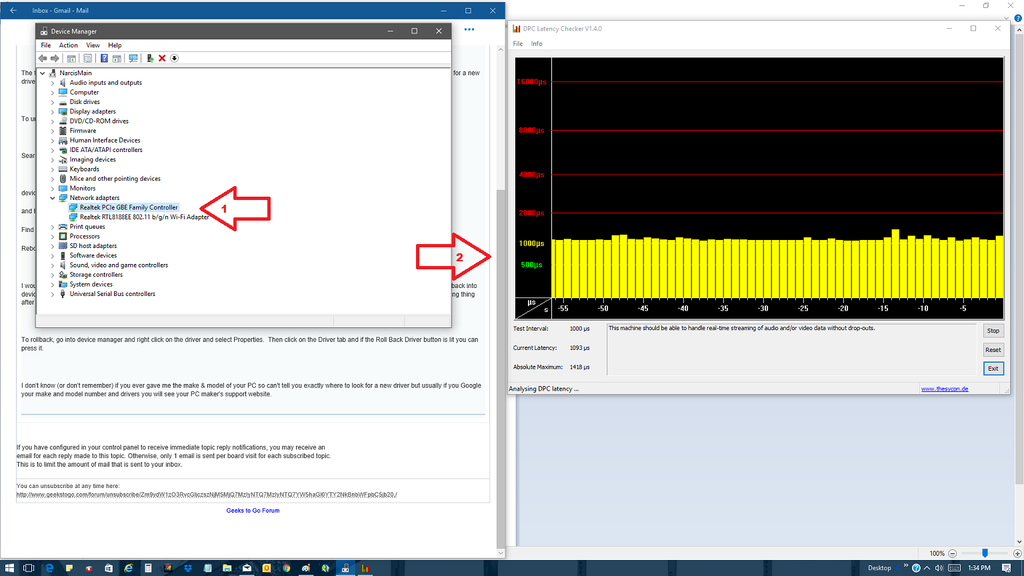
I found it rather quickly.. it was the "Realtek PCIe GBE Family Controller"
=======================================================================
Process CPU Private Bytes Working Set PID Description Company Name Verified Signer
System Idle Process 76.04 0 K 4 K 0
procexp64.exe 15.46 44,924 K 64,756 K 8028 Sysinternals Process Explorer Sysinternals - www.sysinternals.com (Verified) Microsoft Corporation
System 1.01 188 K 10,040 K 4
WmiPrvSE.exe 4,136 K 11,248 K 6880 WMI Provider Host Microsoft Corporation (Verified) Microsoft Windows
dwm.exe 3.68 49,916 K 40,864 K 8960 Desktop Window Manager Microsoft Corporation (Verified) Microsoft Windows
Interrupts 1.23 0 K 0 K n/a Hardware Interrupts and DPCs
csrss.exe 1.01 4,916 K 7,012 K 3884 Client Server Runtime Process Microsoft Corporation (Verified) Microsoft Windows Publisher
chrome.exe 0.18 103,160 K 122,708 K 8148 Google Chrome Google Inc. (Verified) Google Inc
svchost.exe 0.01 77,272 K 74,524 K 556 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
AvastSvc.exe 0.34 104,796 K 40,048 K 1716 avast! Service AVAST Software (Verified) AVAST Software a.s.
svchost.exe 0.04 34,500 K 48,464 K 1296 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
chrome.exe 0.07 65,732 K 108,744 K 7860 Google Chrome Google Inc. (Verified) Google Inc
explorer.exe 0.68 65,552 K 103,784 K 8112 Windows Explorer Microsoft Corporation (Verified) Microsoft Windows
chrome.exe 0.05 83,744 K 108,784 K 5584 Google Chrome Google Inc. (Verified) Google Inc
chrome.exe 0.03 44,976 K 56,228 K 4864 Google Chrome Google Inc. (Verified) Google Inc
SearchIndexer.exe 0.04 34,464 K 23,124 K 1792 Microsoft Windows Search Indexer Microsoft Corporation (Verified) Microsoft Windows
plays_service.exe 0.03 13,164 K 2,596 K 2408 Plays.tv Service Plays.tv, LLC (Verified) Plays.tv
svchost.exe 7,408 K 15,488 K 2196 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
lsass.exe 6,168 K 9,508 K 772 Local Security Authority Process Microsoft Corporation (Verified) Microsoft Windows Publisher
AvastUI.exe 0.02 16,428 K 32,012 K 756 avast! Antivirus AVAST Software (Verified) AVAST Software a.s.
services.exe 3,300 K 4,580 K 764 Services and Controller app Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 18,340 K 21,628 K 420 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 0.02 6,920 K 8,788 K 892 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe < 0.01 10,836 K 15,864 K 840 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
afwServ.exe < 0.01 8,800 K 8,976 K 1480 avast! firewall service AVAST Software (Verified) AVAST Software a.s.
svchost.exe 20,756 K 48,024 K 5404 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe < 0.01 17,488 K 17,004 K 504 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
PhotoshopElementsFileAgent.exe < 0.01 2,704 K 1,336 K 2172 (Verified) Adobe Systems Incorporated
WmiPrvSE.exe 2,352 K 8,404 K 7704 WMI Provider Host Microsoft Corporation (Verified) Microsoft Windows
winlogon.exe 2,100 K 7,320 K 2784 Windows Logon Application Microsoft Corporation (Verified) Microsoft Windows
wininit.exe 1,112 K 2,760 K 652 Windows Start-Up Application Microsoft Corporation (Verified) Microsoft Windows Publisher
unsecapp.exe 1,256 K 6,444 K 6124 Sink to receive asynchronous callbacks for WMI client application Microsoft Corporation (Verified) Microsoft Windows
taskhostw.exe 0.03 7,112 K 19,668 K 5036 Host Process for Windows Tasks Microsoft Corporation (Verified) Microsoft Windows
svchost.exe < 0.01 6,172 K 15,080 K 4752 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 13,500 K 18,756 K 1032 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe < 0.01 4,416 K 6,392 K 2692 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 8,888 K 13,524 K 1148 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 2,688 K 5,788 K 1440 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 3,940 K 2,192 K 2184 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 3,512 K 4,592 K 1552 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 4,940 K 7,304 K 1676 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 1,628 K 3,372 K 3184 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
svchost.exe 2,132 K 3,600 K 2424 Host Process for Windows Services Microsoft Corporation (Verified) Microsoft Windows Publisher
spoolsv.exe 6,796 K 4,084 K 1856 Spooler SubSystem App Microsoft Corporation (Verified) Microsoft Windows
smss.exe 436 K 540 K 400 Windows Session Manager Microsoft Corporation (Verified) Microsoft Windows Publisher
smartscreen.exe 8,100 K 13,680 K 8780 SmartScreen Microsoft Corporation (Verified) Microsoft Windows
sihost.exe 5,780 K 22,328 K 4776 Shell Infrastructure Host Microsoft Corporation (Verified) Microsoft Windows
ShellExperienceHost.exe Suspended 52,640 K 95,760 K 7660 Windows Shell Experience Host Microsoft Corporation (Verified) Microsoft Windows
SettingSyncHost.exe 5,948 K 3,712 K 512 Host Process for Setting Synchronization Microsoft Corporation (Verified) Microsoft Windows
SearchUI.exe Suspended 59,752 K 58,596 K 8980 Search and Cortana application Microsoft Corporation (Verified) Microsoft Windows
RuntimeBroker.exe 29,540 K 41,972 K 5472 Runtime Broker Microsoft Corporation (Verified) Microsoft Windows
RtkAudioService64.exe 1,652 K 2,672 K 1488 Realtek Audio Service Realtek Semiconductor (Verified) Realtek Semiconductor Corp
RichVideo64.exe 1,304 K 1,292 K 2400 RichVideo Module (Verified) CyberLink Corp.
RemindersServer.exe Suspended 8,732 K 18,460 K 5968 Reminders WinRT OOP Server Microsoft Corporation (Verified) Microsoft Windows
RAVBg64.exe 6,016 K 10,868 K 4400 HD Audio Background Process Realtek Semiconductor (Verified) Realtek Semiconductor Corp
procexp.exe 2,884 K 9,816 K 10340 Sysinternals Process Explorer Sysinternals - www.sysinternals.com (Verified) Microsoft Corporation
OSPPSVC.EXE 2,604 K 2,296 K 5024 Microsoft Office Software Protection Platform Service Microsoft Corporation (Verified) Microsoft Corporation
opvapp.exe 1,996 K 7,372 K 1912 (No signature was present in the subject)
OPBHOBrokerDsktop.exe 0.02 2,424 K 1,772 K 5008 HP SimplePass BHO Broker Hewlett-Packard (Verified) Softex Incorporated
OmniServ.exe 3,264 K 2,672 K 1156 HP SimplePass Service Softex Inc. (No signature was present in the subject) Softex Inc.
Memory Compression 244 K 42,564 K 2832
mDNSResponder.exe 1,684 K 2,852 K 2220 Bonjour Service Apple Inc. (Verified) Apple Inc.
ijplmsvc.exe 1,140 K 1,240 K 2228 Inkjet Printer/Scanner/Fax Extended Survey Program Service (Verified) Canon Inc.
HPSupportSolutionsFrameworkService.exe 40,776 K 5,608 K 676 HP Support Solutions Framework Service HP Inc. (Verified) Hewlett-Packard Company
GoogleUpdate.exe 2,092 K 340 K 4064 Google Installer Google Inc. (Verified) Google Inc
GoogleCrashHandler64.exe 1,480 K 564 K 1244 Google Crash Handler Google Inc. (Verified) Google Inc
GoogleCrashHandler.exe 1,640 K 252 K 1012 Google Crash Handler Google Inc. (Verified) Google Inc
fontdrvhost.exe 848 K 3,164 K 8020 Usermode Font Driver Host Microsoft Corporation (Verified) Microsoft Windows
DropboxUpdate.exe 1,936 K 3,548 K 4016 Dropbox Update Dropbox, Inc. (Verified) Dropbox
dasHost.exe 4,412 K 8,872 K 2052 Device Association Framework Provider Host Microsoft Corporation (Verified) Microsoft Windows
csrss.exe 1,548 K 2,736 K 560 Client Server Runtime Process Microsoft Corporation (Verified) Microsoft Windows Publisher
chrome.exe 1,920 K 9,136 K 10404 Google Chrome Google Inc. (Verified) Google Inc
chrome.exe 24,748 K 56,696 K 8836 Google Chrome Google Inc. (Verified) Google Inc
chrome.exe 30,036 K 63,996 K 10548 Google Chrome Google Inc. (Verified) Google Inc
chrome.exe 35,124 K 65,440 K 11084 Google Chrome Google Inc. (Verified) Google Inc
chrome.exe 2,192 K 8,048 K 9600 Google Chrome Google Inc. (Verified) Google Inc
audiodg.exe 13,676 K 19,280 K 7400 Windows Audio Device Graph Isolation Microsoft Corporation (Verified) Microsoft Windows
atiesrxx.exe 1,244 K 1,928 K 1220 AMD External Events Service Module AMD (Verified) Microsoft Windows Hardware Compatibility Publisher
atieclxx.exe 2,064 K 8,220 K 4996 AMD External Events Client Module AMD (Verified) Microsoft Windows Hardware Compatibility Publisher
ApplicationFrameHost.exe 4,680 K 18,340 K 144 Application Frame Host Microsoft Corporation (Verified) Microsoft Windows
Process: System Pid: 4
Type Name
ALPC Port \PowerPort
ALPC Port \PowerMonitorPort
ALPC Port \PdcPort
ALPC Port \SeRmCommandPort
Desktop \Disconnect
Desktop \Disconnect
Directory \GLOBAL??
Directory \Device\Harddisk0
Directory \Device\ClVtDrv
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-155514346-2573954481-755741238-1654018636-1233331829-3075935687-2861478708
Directory \Windows\WindowStations
Directory \Sessions\0\DosDevices\00000000-01592015
Directory \Sessions\0\DosDevices\00000000-000003e4
Directory \Sessions\0\DosDevices\00000000-000003e5
Directory \Device\Http
Directory \Sessions\0\DosDevices\00000000-000d8910
Directory \Sessions\0\DosDevices\00000000-000d8945
Directory \...\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\RPC Control
Directory \...\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433
Directory \...\S-1-15-2-930279079-3258969966-1203931420-3379063298-1496040207-3203565093-3038441310
Directory \...\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\RPC Control
Directory \...\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-95739096-486727260-2033287795-3853587803-1685597119-444378811-2746676523\RPC Control
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433
Directory \...\S-1-15-2-930279079-3258969966-1203931420-3379063298-1496040207-3203565093-3038441310\RPC Control
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\RPC Control
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-350187224-1905355452-1037786396-3028148496-2624191407-3283318427-1255436723\RPC Control
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\RPC Control
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-350187224-1905355452-1037786396-3028148496-2624191407-3283318427-1255436723
Directory \Sessions\0\DosDevices\00000000-014f087d
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-155514346-2573954481-755741238-1654018636-1233331829-3075935687-2861478708\RPC Control
Directory \Sessions\2\AppContainerNamedObjects\S-1-15-2-95739096-486727260-2033287795-3853587803-1685597119-444378811-2746676523
Directory \Sessions\0\DosDevices\00000000-01591fea
Directory \Sessions\2\Windows\WindowStations
Event \EFSInitEvent
Event \UniqueSessionIdEvent
Event \EFSInitEvent
Event \UniqueInteractiveSessionIdEvent
Event \...\DwmComposedEvent_1
Event \BaseNamedObjects\aswstmbfeevnt
Event \BaseNamedObjects\aswstmbferefresh
Event \LanmanServerAnnounceEvent
Event \Sessions\2\BaseNamedObjects\EventShutDownCSRSS
Event \Sessions\2\BaseNamedObjects\DwmComposedEvent_1
File C:\Windows\System32\LogFiles\WMI\Wifi.etl
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTEventLog-System.etl
File \clfs
File \Device\HarddiskVolume5\$Extend\$RmMetadata\$TxfLog\$TxfLog.blf
File \clfs
File \clfs
File \clfs
File D:\$Extend\$RmMetadata\$Txf
File \clfs
File D:\$Extend\$RmMetadata\$TxfLog\$TxfLog.blf
File C:\System Volume Information\{e856424b-67d7-11e6-82fb-0071c20b7792}{3808876b-c176-4e48-b7ae-04046e6cc752}
File C:\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000001
File C:\System Volume Information\{3808876b-c176-4e48-b7ae-04046e6cc752}
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTDiagLog.etl
File C:\$Extend\$RmMetadata\$TxfLog\$TxfLog.blf
File C:\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000003
File \clfs
File \clfs
File C:\$Extend\$RmMetadata\$Txf
File \clfs
File \clfs
File \clfs
File C:\System Volume Information\{98d35562-645a-11e6-82e7-0071c20b7792}{3808876b-c176-4e48-b7ae-04046e6cc752}
File D:\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000001
File D:\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000002
File \clfs
File D:\System Volume Information\{3808876b-c176-4e48-b7ae-04046e6cc752}
File D:\System Volume Information\{98d35563-645a-11e6-82e7-0071c20b7792}{3808876b-c176-4e48-b7ae-04046e6cc752}
File D:\System Volume Information\{e856424e-67d7-11e6-82fb-0071c20b7792}{3808876b-c176-4e48-b7ae-04046e6cc752}
File C:\Windows\System32\drivers\en-US\USBXHCI.SYS.mui
File \Device\HarddiskVolume5\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000001
File \Device\HarddiskVolume5\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000002
File \Device\HarddiskVolume5\$Extend\$RmMetadata\$Txf
File \clfs
File \clfs
File \clfs
File \clfs
File \Device\HarddiskVolume1\$Extend\$RmMetadata\$TxfLog\$TxfLog.blf
File \Device\HarddiskVolume1\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000001
File \Device\HarddiskVolume1\$Extend\$RmMetadata\$TxfLog\$TxfLogContainer00000000000000000002
File \clfs
File \clfs
File \Device\HarddiskVolume1\$Extend\$RmMetadata\$Txf
File \clfs
File \clfs
File \clfs
File C:\Windows\System32\config\SOFTWARE
File C:\Windows\System32\config\SOFTWARE.LOG1
File C:\Windows\System32\config\SOFTWARE.LOG2
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTUBPM.etl
File C:\Windows\System32\config\SYSTEM
File C:\Windows\System32\config\SYSTEM.LOG1
File C:\Windows\System32\config\SYSTEM.LOG2
File C:\Windows\System32\config\TxR\{f5b13570-4b48-11e6-80cb-e41d2d012050}.TM.blf
File C:\Windows\System32\config\RegBack\SAM
File C:\Windows\System32\config\TxR\{f5b13570-4b48-11e6-80cb-e41d2d012050}.TMContainer00000000000000000001.regtrans-ms
File C:\Windows\System32\config\TxR\{f5b13570-4b48-11e6-80cb-e41d2d012050}.TMContainer00000000000000000002.regtrans-ms
File C:\hiberfil.sys
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTEventlog-Security.etl
File \clfs
File \clfs
File C:\Windows\System32\WDI\LogFiles\WdiContextLog.etl.002
File C:\Windows\bootstat.dat
File \Device\KsecDD
File \Device\KsecDD
File C:\pagefile.sys
File C:\Windows\System32\config\DEFAULT.LOG2
File C:\Windows\System32\config\DEFAULT
File C:\swapfile.sys
File C:\Windows\System32\config\DEFAULT.LOG1
File C:\Windows\System32\en-US\win32kbase.sys.mui
File C:\Users\NiTa\AppData\Local\Microsoft\Windows\UsrClass.dat{dd435084-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000002.regtrans-ms
File C:\Program Files (x86)\Adobe\Photoshop Elements 6.0\Required\ADMUI3.fon
File C:\Program Files (x86)\Common Files\Microsoft Shared\EQUATION\MTEXTRA.TTF
File \Device\Ndis
File \Device\aswSnx
File C:\Users\NiTa\NTUSER.DAT{dd434f3b-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000002.regtrans-ms
File C:\Windows\System32\config\SECURITY.LOG1
File C:\Windows\System32\config\SECURITY
File C:\Windows\System32\config\SECURITY.LOG2
File C:\Windows\System32\config\SAM
File C:\Windows\System32\config\SAM.LOG1
File C:\Windows\System32\config\SAM.LOG2
File C:\Windows\System32\SleepStudy\UserNotPresentSession.etl
File \clfs
File C:\Windows\ServiceProfiles\NetworkService\NTUSER.DAT.LOG2
File C:\Windows\ServiceProfiles\NetworkService\NTUSER.DAT{f5b13604-4b48-11e6-80cb-e41d2d012050}.TM.blf
File C:\Windows\ServiceProfiles\NetworkService\NTUSER.DAT
File C:\Windows\ServiceProfiles\NetworkService\NTUSER.DAT.LOG1
File C:\Windows\ServiceProfiles\NetworkService\NTUSER.DAT{f5b13604-4b48-11e6-80cb-e41d2d012050}.TMContainer00000000000000000001.regtrans-ms
File C:\Windows\ServiceProfiles\NetworkService\NTUSER.DAT{f5b13604-4b48-11e6-80cb-e41d2d012050}.TMContainer00000000000000000002.regtrans-ms
File \clfs
File \clfs
File C:\Windows\System32\config\BBI
File C:\Windows\System32\config\BBI.LOG1
File C:\Windows\System32\config\BBI.LOG2
File C:\Windows\ServiceProfiles\LocalService\NTUSER.DAT{dd434f19-625f-11e6-b28a-f3afb8f9ba47}.TM.blf
File C:\Windows\ServiceProfiles\LocalService\NTUSER.DAT
File C:\Windows\ServiceProfiles\LocalService\NTUSER.DAT.LOG1
File C:\Windows\ServiceProfiles\LocalService\NTUSER.DAT.LOG2
File \clfs
File C:\Windows\ServiceProfiles\LocalService\NTUSER.DAT{dd434f19-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000001.regtrans-ms
File C:\Windows\ServiceProfiles\LocalService\NTUSER.DAT{dd434f19-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000002.regtrans-ms
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTEventLog-Application.etl
File \Device\HarddiskVolume4
File \Device\Tcp
File \Device\Tcp
File \Device\NamedPipe\afwCallbackPipe2
File C:\ProgramData\Microsoft\Windows\AppRepository\Packages\Microsoft.Windows.ShellExperienceHost_10.0.14393.0_neutral_neutral_cw5n1h2txyewy\ActivationStore.dat.LOG2
File \Device\Mup
File \Device\Mup
File \Device\Tcp
File C:\ProgramData\Microsoft\Windows\wfp\wfpdiag.etl
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTWFP-IPsec Diagnostics.etl
File \Device\NamedPipe\afwCallbackPipe3
File C:\Windows\System32\config\TxR\{f5b1356f-4b48-11e6-80cb-e41d2d012050}.TxR.0.regtrans-ms
File C:\Windows\appcompat\Programs\Amcache.hve
File \Device\Tcp
File C:\Windows\System32\config\TxR\{f5b1356f-4b48-11e6-80cb-e41d2d012050}.TxR.1.regtrans-ms
File \Device\NamedPipe\
File \Device\NamedPipe\
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTDiagtrack-Listener.etl
File C:\Windows\appcompat\Programs\Amcache.hve.LOG1
File C:\Windows\appcompat\Programs\Amcache.hve.LOG2
File C:\Windows\System32\config\TxR\{f5b1356f-4b48-11e6-80cb-e41d2d012050}.TxR.blf
File C:\Windows\System32\config\TxR\{f5b1356f-4b48-11e6-80cb-e41d2d012050}.TxR.2.regtrans-ms
File \clfs
File \Device\NamedPipe
File C:\ProgramData\AVAST Software\Avast\Fonts\OpenSans-Light.ttf
File \Device\00000037
File \Device\NamedPipe
File C:\Windows\System32\LogFiles\WMI\LwtNetLog.etl
File C:\Windows\Logs\dosvc\dosvc.20160824_092038_680.etl
File \Device\NamedPipe
File \Device\NamedPipe
File C:\ProgramData\Microsoft\Windows\AppRepository\Packages\Microsoft.Windows.Cortana_1.7.0.14393_neutral_neutral_cw5n1h2txyewy\ActivationStore.dat
File C:\Windows\System32\config\RegBack\SOFTWARE
File C:\Users\HeatherAnnique\NTUSER.DAT{dd434f3b-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000001.regtrans-ms
File C:\ProgramData\Microsoft\Windows\AppRepository\Packages\Microsoft.Windows.Cortana_1.7.0.14393_neutral_neutral_cw5n1h2txyewy\ActivationStore.dat.LOG2
File C:\Users\HeatherAnnique\NTUSER.DAT
File \Device\0000003c
File C:\Users\NiTa\AppData\Local\Packages\Microsoft.Windows.ShellExperienceHost_cw5n1h2txyewy\Settings\settings.dat.LOG2
File \Device\NamedPipe
File C:\Users\NiTa\AppData\Local\Microsoft\Windows\UsrClass.dat
File C:\Users\NiTa\AppData\Local\Packages\Microsoft.Windows.ShellExperienceHost_cw5n1h2txyewy\Settings\settings.dat.LOG1
File \Device\HarddiskVolume2\EFI\Microsoft\Boot\BCD
File C:\ProgramData\AVAST Software\Avast\Fonts\OpenSans-Bold.ttf
File \clfs
File C:\Windows\System32\winevt\Logs\DebugChannel.etl
File \Device\0000003d
File C:\ProgramData\AVAST Software\Avast\Fonts\RobotoCondensed-Regular.ttf
File C:\Windows\System32\config\RegBack\SECURITY
File C:\Users\HeatherAnnique\ntuser.dat.LOG1
File C:\ProgramData\AVAST Software\Avast\Fonts\OpenSans-Italic.ttf
File C:\ProgramData\Microsoft\Windows\AppRepository\Packages\Microsoft.Windows.ShellExperienceHost_10.0.14393.0_neutral_neutral_cw5n1h2txyewy\ActivationStore.dat.LOG1
File C:\ProgramData\Microsoft\Windows\AppRepository\Packages\Microsoft.Windows.Cortana_1.7.0.14393_neutral_neutral_cw5n1h2txyewy\ActivationStore.dat.LOG1
File C:\Users\NiTa\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\Settings\settings.dat.LOG1
File C:\Users\NiTa\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1
File \Device\HarddiskVolume4
File C:\ProgramData\AVAST Software\Avast\Fonts\RobotoCondensed-Bold.ttf
File C:\Users\NiTa\AppData\Local\Packages\Microsoft.Windows.ShellExperienceHost_cw5n1h2txyewy\Settings\settings.dat
File C:\Users\NiTa\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\Settings\settings.dat.LOG2
File C:\ProgramData\AVAST Software\Avast\Fonts\OpenSans-Regular.ttf
File \Device\HarddiskVolume2\EFI\Microsoft\Boot\BCD.LOG
File C:\Users\HeatherAnnique\NTUSER.DAT{dd434f3b-625f-11e6-b28a-f3afb8f9ba47}.TM.blf
File C:\Windows\System32\config\RegBack\SYSTEM
File C:\Users\NiTa\AppData\Local\Microsoft\Windows\UsrClass.dat{dd435084-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000001.regtrans-ms
File C:\Users\HeatherAnnique\ntuser.dat.LOG2
File C:\Users\HeatherAnnique\NTUSER.DAT{dd434f3b-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000002.regtrans-ms
File C:\Windows\System32\config\RegBack\DEFAULT
File C:\Users\NiTa\ntuser.dat.LOG2
File C:\Users\NiTa\NTUSER.DAT{dd434f3b-625f-11e6-b28a-f3afb8f9ba47}.TMContainer00000000000000000001.regtrans-ms
File \clfs
File C:\Users\NiTa\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG2
File C:\Users\NiTa\NTUSER.DAT{dd434f3b-625f-11e6-b28a-f3afb8f9ba47}.TM.blf
File C:\Users\NiTa\NTUSER.DAT
File C:\Users\NiTa\AppData\Local\Microsoft\Windows\UsrClass.dat{dd435084-625f-11e6-b28a-f3afb8f9ba47}.TM.blf
File \clfs
File \Device\NamedPipe
File C:\Users\NiTa\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\Settings\settings.dat
File \Device\NamedPipe
File \clfs
File C:\Program Files (x86)\Common Files\Microsoft Shared\EQUATION\MTEXTRA.TTF
File C:\Users\NiTa\ntuser.dat.LOG1
File \clfs
File \Device\NamedPipe
File C:\Program Files (x86)\Adobe\Photoshop Elements 6.0\Required\ADMUI3.fon
File C:\ProgramData\Microsoft\Windows\AppRepository\Packages\Microsoft.Windows.ShellExperienceHost_10.0.14393.0_neutral_neutral_cw5n1h2txyewy\ActivationStore.dat
File \clfs
File C:\Windows\System32\LogFiles\WMI\RtBackup\EtwRTPROCEXP TRACE.etl
FilterConnectionPort \SnxVlabCommPort
FilterConnectionPort \SnxCommPort
FilterConnectionPort \aswFsBlkPort
FilterConnectionPort \storqosfltport
FilterConnectionPort \WcnfsPort
FilterConnectionPort \WcifsPort
FilterConnectionPort \aswPort
Key \REGISTRY
Key HKLM\SYSTEM\ControlSet001\Control\hivelist
Key HKLM\SYSTEM\ControlSet001\Control\Session Manager\Memory Management\PrefetchParameters
Key HKLM\SYSTEM\ControlSet001\Control\Notifications
Key HKLM\SYSTEM\Setup
Key HKLM\SYSTEM
Key HKLM\SYSTEM\ControlSet001
Key HKLM\SYSTEM\DriverDatabase
Key HKU
Key HKLM\SYSTEM\ControlSet001\Control\DeviceClasses
Key HKLM\SYSTEM\ControlSet001\Enum
Key HKLM\SYSTEM\ControlSet001\Control\DeviceContainers
Key HKLM\SYSTEM\ControlSet001\Control\Class
Key HKLM\SYSTEM\ControlSet001\Services
Key HKLM\SYSTEM\ControlSet001\Services\NDIS\IfTypes\131
Key HKLM\SYSTEM\ControlSet001\Control\WMI\Security
Key HKLM\SYSTEM\RNG
Key HKLM\SYSTEM\ControlSet001\Services\NDIS\IfTypes\23
Key HKLM\SYSTEM\ControlSet001\Services\NDIS\IfTypes\24
Key HKLM\SYSTEM\ControlSet001\Services\NDIS\IfTypes\6
Key HKLM\SYSTEM\ControlSet001\Services\aswSP
Key HKLM\SYSTEM\ControlSet001\Services\aswSnx
Key HKLM\SYSTEM\ControlSet001\Control\FileSystem
Key HKLM\SYSTEM\ControlSet001\Control\Power\Profile\Events\{54533251-82be-4824-96c1-47b60b740d00}\{0DA965DC-8FCF-4c0b-8EFE-8DD5E7BC959A}\{7E01ADEF-81E6-4e1b-8075-56F373584694}
Key HKLM\SYSTEM\ControlSet001\Control\Power\Profile\Events\{54533251-82be-4824-96c1-47b60b740d00}\{EE1E4F72-E368-46b1-B3C6-5048B11C2DBD}\{9C1F0DBA-33E9-43af-9EDA-A607AA5139DA}
Key HKLM\SYSTEM\ControlSet001\Control\FileSystem
Key HKLM\SYSTEM\ControlSet001\Policies
Key HKLM\SYSTEM\ControlSet001\Services\NDIS\IfTypes\71
Key HKLM\HARDWARE\DEVICEMAP\Scsi\Scsi Port 0\Scsi Bus 0
Key HKLM\HARDWARE\DEVICEMAP\Scsi\Scsi Port 0\Scsi Bus 1
Key HKLM\SYSTEM\ControlSet001\Services\Mup
Key HKLM\SYSTEM\ControlSet001\Control\NetworkProvider\Order
Key HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options
Key HKLM\SYSTEM\ControlSet001\Control\Lsa
Key HKLM\SYSTEM\ControlSet001\Control\Lsa
Key HKLM\SOFTWARE\Policies\Microsoft\Windows
Key HKLM\SYSTEM\ControlSet001\Control\{7746D80F-97E0-4E26-9543-26B41FC22F79}\{221601AB-48C7-4970-B0EC-96E66F578407}
Key HKLM\SYSTEM\ControlSet001\Control\{7746D80F-97E0-4E26-9543-26B41FC22F79}\{FB9F5B62-B48B-45F5-8586-E514958C92E2}
Key HKLM\SYSTEM\ControlSet001\Control\{7746D80F-97E0-4E26-9543-26B41FC22F79}\{498B1B9F-8618-4E6C-9AD1-6A759BFBFB23}
Key HKLM\SYSTEM\ControlSet001\Services\Dfsc\Parameters
Key HKLM\SYSTEM\ControlSet001\Control\{7746D80F-97E0-4E26-9543-26B41FC22F79}\{D73E01AC-F5A0-4D80-928B-33C1920C38BA}
Key HKLM\SYSTEM\ControlSet001\Control\{7746D80F-97E0-4E26-9543-26B41FC22F79}\{59AEE675-B203-4D61-9A1F-04518A20F359}
Key HKLM\SYSTEM\ControlSet001\Control\{7746D80F-97E0-4E26-9543-26B41FC22F79}\{A25AE4F2-1B96-4CED-8007-AA30E9B1A218}
Key HKLM\SYSTEM\ControlSet001\Control\FileSystem
Key HKLM\SYSTEM\ControlSet001\Control\hiveredirectionlist
Key HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Notifications
Key HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Notifications\Data
Key HKLM\SYSTEM\ControlSet001\Control\Class\{4d36e97d-e325-11ce-bfc1-08002be10318}\0042
Key HKLM\SYSTEM\ControlSet001\Control\Class\{4d36e96e-e325-11ce-bfc1-08002be10318}\0001
Key HKLM\SYSTEM\ControlSet001\Control\Class\{4d36e96e-e325-11ce-bfc1-08002be10318}\0001
Key HKLM\SYSTEM\ControlSet001\Control\Class\{4d36e96e-e325-11ce-bfc1-08002be10318}\0001
Key HKLM\SYSTEM\ControlSet001\Control\Session Manager\Quota System
Key HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\VolatileNotifications
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy\State\Machine
Key HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy\State\Machine
Key HKLM\SYSTEM\ControlSet001\Services\NativeWifiP
Key HKLM\SYSTEM\ControlSet001\Services\NativeWifiP\Parameters
Key HKLM\SYSTEM\ControlSet001\Services\NativeWifiP\Parameters\Adapters
Key HKLM\SYSTEM\ControlSet001\Services\HTTP\Parameters\UrlAclInfo
Key HKLM\SYSTEM\ControlSet001\Services\NativeWifiP\Parameters\Adapters\{10fdea08-1168-4f59-b05d-e7c23af3e1b4}\WFD
Key HKLM\SYSTEM\ControlSet001\Services\NativeWifiP\Parameters\Adapters\{10fdea08-1168-4f59-b05d-e7c23af3e1b4}\WFDMib
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{10fdea08-1168-4f59-b05d-e7c23af3e1b4}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{256469c7-09ae-428e-ae11-1c7360cf89b6}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{469b8358-7c69-4cc4-8b82-af4310768011}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{7e979084-3c51-496d-8a2c-f361b4e39318}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{8332e81f-a923-431a-8ebc-b3e311f671e5}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{8718928d-cbeb-45ea-a621-800a9249001d}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{dd434edb-625f-11e6-b28a-806e6f6e6963}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{e630b5b7-d1e5-4d84-ba7f-5965f9e1f034}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\Interfaces\{eeb093a2-d0b2-4795-aeda-bf16a4ecdede}
Key HKLM\SYSTEM\ControlSet001\Services\Tcpip\Parameters\PersistentRoutes
Key HKLM\SYSTEM\ControlSet001\Control\CoDeviceInstallers
Key HKLM\SYSTEM\DriverDatabase\DriverInfFiles
Key HKLM\SYSTEM\DriverDatabase\DriverPackages
Key HKLM\SYSTEM\ControlSet001\Control\ProductOptions
Key HKLM\SOFTWARE\Policies\Microsoft\Windows\NetworkProvider\HardenedPaths
Key HKLM\SYSTEM\DriverDatabase\DeviceIds
Key HKCU\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
Key HKLM\SYSTEM\ControlSet001\Services\NativeWifiP\Parameters\Adapters\{469b8358-7c69-4cc4-8b82-af4310768011}\ExtSTAMib
Key HKLM\SYSTEM\ControlSet001\Services\NativeWifiP\Parameters\Adapters\{469b8358-7c69-4cc4-8b82-af4310768011}\ExtSTA
Mutant \KernelObjects\BcdSyncMutant
Partition \KernelObjects\MemoryPartition0
Process System(4)
Process smss.exe(400)
Process chrome.exe(10548)
Process System(4)
Process smss.exe(400)
Process explorer.exe(8112)
Process procexp.exe(10340)
Process csrss.exe(560)
Process csrss.exe(560)
Process csrss.exe(560)
Process wininit.exe(652)
Process wininit.exe(652)
Process explorer.exe(8112)
Process svchost.exe(504)
Process svchost.exe(1032)
Process svchost.exe(504)
Process OmniServ.exe(1156)
Process atiesrxx.exe(1220)
Process lsass.exe(772)
Process lsass.exe(772)
Process services.exe(764)
Process services.exe(764)
Process lsass.exe(772)
Process lsass.exe(772)
Process lsass.exe(772)
Process ShellExperienceHost.exe(7660)
Process svchost.exe(840)
Process svchost.exe(840)
Process services.exe(764)
Process svchost.exe(840)
Process svchost.exe(840)
Process svchost.exe(892)
Process svchost.exe(892)
Process wininit.exe(652)
Process svchost.exe(840)
Process smartscreen.exe(8780)
Process svchost.exe(840)
Process svchost.exe(504)
Process svchost.exe(420)
Process svchost.exe(556)
Process svchost.exe(504)
Process atiesrxx.exe(1220)
Process atiesrxx.exe(1220)
Process OmniServ.exe(1156)
Process svchost.exe(1032)
Process OmniServ.exe(1156)
Process svchost.exe(1148)
Process OmniServ.exe(1156)
Process RtkAudioService64.exe(1488)
Process svchost.exe(1296)
Process RtkAudioService64.exe(1488)
Process svchost.exe(1296)
Process RtkAudioService64.exe(1488)
Process svchost.exe(556)
Process svchost.exe(1296)
Process svchost.exe(1296)
Process svchost.exe(1440)
Process svchost.exe(1440)
Process svchost.exe(1552)
Process svchost.exe(1552)
Process svchost.exe(1552)
Process svchost.exe(1552)
Process svchost.exe(1552)
Process svchost.exe(1552)
Process svchost.exe(1552)
Process svchost.exe(2184)
Process AvastSvc.exe(1716)
Process svchost.exe(840)
Process AvastSvc.exe(1716)
Process svchost.exe(1676)
Process AvastSvc.exe(1716)
Process AvastSvc.exe(1716)
Process spoolsv.exe(1856)
Process svchost.exe(556)
Process spoolsv.exe(1856)
Process spoolsv.exe(1856)
Process svchost.exe(1148)
Process SearchUI.exe(8980)
Process afwServ.exe(1480)
Process afwServ.exe(1480)
Process afwServ.exe(1480)
Process svchost.exe(420)
Process svchost.exe(420)
Process dasHost.exe(2052)
Process afwServ.exe(1480)
Process Memory Compression(2832)
Process dasHost.exe(2052)
Process PhotoshopElementsFileAgent.exe(2172)
Process RichVideo64.exe(2400)
Process PhotoshopElementsFileAgent.exe(2172)
Process PhotoshopElementsFileAgent.exe(2172)
Process mDNSResponder.exe(2220)
Process svchost.exe(2196)
Process svchost.exe(2692)
Process ijplmsvc.exe(2228)
Process ijplmsvc.exe(2228)
Process ijplmsvc.exe(2228)
Process mDNSResponder.exe(2220)
Process svchost.exe(2692)
Process svchost.exe(556)
Process svchost.exe(2692)
Process svchost.exe(1296)
Process ijplmsvc.exe(2228)
Process mDNSResponder.exe(2220)
Process RichVideo64.exe(2400)
Process svchost.exe(420)
Process svchost.exe(1296)
Process svchost.exe(1296)
Process PhotoshopElementsFileAgent.exe(2172)
Process svchost.exe(2424)
Process plays_service.exe(2408)
Process plays_service.exe(2408)
Process plays_service.exe(2408)
Process svchost.exe(2184)
Process svchost.exe(2692)
Process RichVideo64.exe(2400)
Process svchost.exe(2196)
Process svchost.exe(2196)
Process svchost.exe(1296)
Process plays_service.exe(2408)
Process svchost.exe(2692)
Process svchost.exe(2692)
Process svchost.exe(2692)
Process svchost.exe(2692)
Process svchost.exe(2196)
Process svchost.exe(2692)
Process svchost.exe(2692)
Process svchost.exe(504)
Process services.exe(764)
Process GoogleCrashHandler64.exe(1244)
Process svchost.exe(3184)
Process dasHost.exe(2052)
Process svchost.exe(3184)
Process svchost.exe(5404)
Process svchost.exe(2692)
Process dasHost.exe(2052)
Process dasHost.exe(2052)
Process dasHost.exe(2052)
Process svchost.exe(1296)
Process dasHost.exe(2052)
Process chrome.exe(7860)
Process dasHost.exe(2052)
Process audiodg.exe(7400)
Process DropboxUpdate.exe(4016)
Process dasHost.exe(2052)
Process GoogleCrashHandler.exe(1012)
Process ShellExperienceHost.exe(7660)
Process svchost.exe(840)
Process svchost.exe(840)
Process svchost.exe(1296)
Process GoogleUpdate.exe(4064)
Process SearchUI.exe(8980)
Process GoogleUpdate.exe(4064)
Process HPSupportSolutionsFrameworkService.exe(676)
Process procexp64.exe(8028)
Process chrome.exe(5584)
Process GoogleUpdate.exe(4064)
Process GoogleCrashHandler64.exe(1244)
Process atieclxx.exe(4996)
Process svchost.exe(4752)
Process DropboxUpdate.exe(4016)
Process dasHost.exe(2052)
Process RAVBg64.exe(4400)
Process taskhostw.exe(5036)
Process svchost.exe(1296)
Process svchost.exe(840)
Process spoolsv.exe(1856)
Process spoolsv.exe(1856)
Process spoolsv.exe(1856)
Process spoolsv.exe(1856)
Process spoolsv.exe(1856)
Process spoolsv.exe(1856)
Process svchost.exe(1296)
Process svchost.exe(1296)
Process GoogleCrashHandler64.exe(1244)
Process SearchUI.exe(8980)
Process HPSupportSolutionsFrameworkService.exe(676)
Process DropboxUpdate.exe(4016)
Process svchost.exe(1296)
Process GoogleCrashHandler.exe(1012)
Process GoogleCrashHandler.exe(1012)
Process unsecapp.exe(6124)
Process HPSupportSolutionsFrameworkService.exe(676)
Process GoogleCrashHandler.exe(1012)
Process chrome.exe(7860)
Process SearchIndexer.exe(1792)
Process SearchIndexer.exe(1792)
Process fontdrvhost.exe(8020)
Process svchost.exe(5404)
Process chrome.exe(10404)
Process smartscreen.exe(8780)
Process chrome.exe(8836)
Process svchost.exe(1032)
Process svchost.exe(1032)
Process svchost.exe(1032)
Process winlogon.exe(2784)
Process chrome.exe(8148)
Process svchost.exe(1032)
Process svchost.exe(1296)
Process dasHost.exe(2052)
Process atieclxx.exe(4996)
Process svchost.exe(5404)
Process procexp64.exe(8028)
Process procexp.exe(10340)
Process SearchUI.exe(8980)
Process OPBHOBrokerDsktop.exe(5008)
Process fontdrvhost.exe(8020)
Process chrome.exe(11084)
Process OSPPSVC.EXE(5024)
Process OSPPSVC.EXE(5024)
Process svchost.exe(1032)
Process dasHost.exe(2052)
Process procexp.exe(10340)
Process chrome.exe(4864)
Process chrome.exe(11084)
Process WmiPrvSE.exe(6880)
Process svchost.exe(1032)
Process chrome.exe(5584)
Process RemindersServer.exe(5968)
Process chrome.exe(8836)
Process svchost.exe(1032)
Process AvastUI.exe(756)
Process explorer.exe(8112)
Process svchost.exe(5404)
Process OSPPSVC.EXE(5024)
Process AvastUI.exe(756)
Process RAVBg64.exe(4400)
Process SearchUI.exe(8980)
Process dasHost.exe(2052)
Process ApplicationFrameHost.exe(144)
Process chrome.exe(8836)
Process unsecapp.exe(6124)
Process chrome.exe(4864)
Process chrome.exe(9600)
Process chrome.exe(10404)
Process chrome.exe(10548)
Process chrome.exe(11084)
Process chrome.exe(10548)
Process procexp64.exe(8028)
Process chrome.exe(4864)
Process chrome.exe(8148)
Process audiodg.exe(7400)
Process audiodg.exe(7400)
Process chrome.exe(7860)
Process AvastUI.exe(756)
Process RAVBg64.exe(4400)
Process SettingSyncHost.exe(512)
Process svchost.exe(2692)
Process svchost.exe(5404)
Process winlogon.exe(2784)
Process svchost.exe(1032)
Process svchost.exe(1032)
Process winlogon.exe(2784)
Process svchost.exe(1032)
Process svchost.exe(5404)
Process ShellExperienceHost.exe(7660)
Process WmiPrvSE.exe(7704)
Process dwm.exe(8960)
Process sihost.exe(4776)
Process RuntimeBroker.exe(5472)
Process OPBHOBrokerDsktop.exe(5008)
Process chrome.exe(7860)
Process WmiPrvSE.exe(7704)
Process svchost.exe(5404)
Process AvastUI.exe(756)
Process OPBHOBrokerDsktop.exe(5008)
Process opvapp.exe(1912)
Process svchost.exe(1296)
Process chrome.exe(9600)
Process sihost.exe(4776)
Process chrome.exe(5584)
Process RuntimeBroker.exe(5472)
Process WmiPrvSE.exe(6880)
Process dasHost.exe(2052)
Process RemindersServer.exe(5968)
Process svchost.exe(1032)
Process ApplicationFrameHost.exe(144)
Process dasHost.exe(2052)
Process svchost.exe(1032)
Process dasHost.exe(2052)
Process svchost.exe(1032)
Process svchost.exe(5404)
Process svchost.exe(1032)
Process dasHost.exe(2052)
Process dasHost.exe(2052)
Process dasHost.exe(2052)
Process dasHost.exe(2052)
Process svchost.exe(1032)
Process taskhostw.exe(5036)
Process SettingSyncHost.exe(512)
Process procexp64.exe(8028)
Process svchost.exe(1032)
Process chrome.exe(7860)
Process svchost.exe(1296)
Process dasHost.exe(2052)
Process svchost.exe(1032)
Process csrss.exe(3884)
Process opvapp.exe(1912)
Process smartscreen.exe(8780)
Process chrome.exe(8148)
Section \Win32kCrossSessionGlobals
Section \Device\PhysicalMemory
Section \Device\PhysicalMemory
Session \KernelObjects\Session0
Session \KernelObjects\Session2
Session \KernelObjects\Session2
Session \KernelObjects\Session2
Session \KernelObjects\Session2
Session \KernelObjects\Session2
Session \KernelObjects\Session2
Session \KernelObjects\Session2
Session \KernelObjects\Session2
Session \KernelObjects\Session2
SymbolicLink \GLOBAL??\ACPI#AuthenticAMD_-_AMD64_Family_22_Model_0_-_AMD_E1-6015_APU_with_Radeon™_HD_Graphics____#_2#{dbe4373d-3c81-40cb-ace4-e0e5d05f0c9f}
SymbolicLink \GLOBAL??\ACPI#PNP0C0C#aa#{4afa3d53-74a7-11d0-be5e-00a0c9062857}
SymbolicLink \GLOBAL??\ACPI#FixedButton#2&daba3ff&3#{4afa3d53-74a7-11d0-be5e-00a0c9062857}
SymbolicLink \GLOBAL??\ACPI#AuthenticAMD_-_AMD64_Family_22_Model_0_-_AMD_E1-6015_APU_with_Radeon™_HD_Graphics____#_2#{97fadb10-4e33-40ae-359c-8bef029dbdd0}
SymbolicLink \GLOBAL??\PCI#VEN_1022&DEV_7814&SUBSYS_2B56103C&REV_01#3&11583659&0&80#{3abf6f2d-71c4-462a-8a92-1e6861e6af27}
SymbolicLink \GLOBAL??\ROOT#MEDIA#0000#{65e8773d-8f56-11d0-a3b9-00a0c9223196}
SymbolicLink \GLOBAL??\ROOT#MEDIA#0000#{6994ad05-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\ROOT#SYSTEM#0000#{ffbb6e3f-ccfe-4d84-90d9-421418b03a8e}
SymbolicLink \GLOBAL??\ROOT#SYSTEM#0000#{cf1dda2c-9743-11d0-a3ee-00a0c9223196}
SymbolicLink \GLOBAL??\ROOT#SYSTEM#0000#{97ebaacb-95bd-11d0-a3ea-00a0c9223196}
SymbolicLink \GLOBAL??\ROOT#SYSTEM#0000#{53172480-4791-11d0-a5d6-28db04c10000}
SymbolicLink \GLOBAL??\ROOT#SYSTEM#0000#{0a4252a0-7e70-11d0-a5d6-28db04c10000}
SymbolicLink \GLOBAL??\PCI#VEN_1022&DEV_7807&SUBSYS_2B56103C&REV_39#3&11583659&0&98#{3abf6f2d-71c4-462a-8a92-1e6861e6af27}
SymbolicLink \GLOBAL??\PCI#VEN_1022&DEV_7808&SUBSYS_2B56103C&REV_39#3&11583659&0&9A#{3abf6f2d-71c4-462a-8a92-1e6861e6af27}
SymbolicLink \GLOBAL??\PCI#VEN_1022&DEV_7808&SUBSYS_2B56103C&REV_39#3&11583659&0&92#{3abf6f2d-71c4-462a-8a92-1e6861e6af27}
SymbolicLink \GLOBAL??\PCI#VEN_1022&DEV_7807&SUBSYS_2B56103C&REV_39#3&11583659&0&90#{3abf6f2d-71c4-462a-8a92-1e6861e6af27}
SymbolicLink \GLOBAL??\ROOT#vdrvroot#0000#{2e34d650-5819-42ca-84ae-d30803bae505}
SymbolicLink \GLOBAL??\ROOT#spaceport#0000#{53f5630e-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\ROOT#spaceport#0000#{ef66a56f-88d1-4cd8-98c4-49faf57ad8af}
SymbolicLink \GLOBAL??\ROOT#volmgr#0000#{53f5630e-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\PCI#VEN_1022&DEV_7801&SUBSYS_2B56103C&REV_40#3&11583659&0&88#{2accfe60-c130-11d2-b082-00a0c91efb8b}
SymbolicLink \GLOBAL??\SCSI#Disk&Ven_&Prod_ST1000DM003-1ER1#4&35dce77&0&000000#{53f56307-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\STORAGE#Volume#{f99d45b9-fb89-11e4-8251-806e6f6e6963}#0000000056800000#{7f108a28-9833-4b3b-b780-2c6b5fa5c062}
SymbolicLink \GLOBAL??\STORAGE#Volume#{f99d45b9-fb89-11e4-8251-806e6f6e6963}#0000000040000000#{7f108a28-9833-4b3b-b780-2c6b5fa5c062}
SymbolicLink \GLOBAL??\STORAGE#Volume#{f99d45b9-fb89-11e4-8251-806e6f6e6963}#0000000000100000#{53f5630d-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\STORAGE#Volume#{f99d45b9-fb89-11e4-8251-806e6f6e6963}#000000005E800000#{53f5630d-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\STORAGE#Volume#{f99d45b9-fb89-11e4-8251-806e6f6e6963}#000000E415200000#{53f5630d-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\STORAGE#Volume#{f99d45b9-fb89-11e4-8251-806e6f6e6963}#000000E431400000#{53f5630d-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\ROOT#UMBUS#0000#{65a9a6cf-64cd-480b-843e-32c86e1ba19f}
SymbolicLink \GLOBAL??\SCSI#CdRom&Ven_hp&Prod_DVDRAM_GUB0N#4&35dce77&0&010000#{53f56308-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\SCSI#CdRom&Ven_hp&Prod_DVDRAM_GUB0N#4&35dce77&0&010000#{53f5630d-b6bf-11d0-94f2-00a0c91efb8b}
SymbolicLink \GLOBAL??\ROOT#SYSTEM#0000#{3c0d501a-140b-11d1-b40f-00a0c9223196}
SymbolicLink \GLOBAL??\ROOT#SYSTEM#0000#{4747b320-62ce-11cf-a5d6-28db04c10000}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{65e8773d-8f56-11d0-a3b9-00a0c9223196}
SymbolicLink \GLOBAL??\ACPI#AuthenticAMD_-_AMD64_Family_22_Model_0_-_AMD_E1-6015_APU_with_Radeon™_HD_Graphics____#_1#{97fadb10-4e33-40ae-359c-8bef029dbdd0}
SymbolicLink \GLOBAL??\ACPI#AuthenticAMD_-_AMD64_Family_22_Model_0_-_AMD_E1-6015_APU_with_Radeon™_HD_Graphics____#_1#{dbe4373d-3c81-40cb-ace4-e0e5d05f0c9f}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{eb115ffc-10c8-4964-831d-6dcb02e6f23f}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{dda54a40-1e4c-11d1-a050-405705c10000}
SymbolicLink \GLOBAL??\USB#ROOT_HUB#4&1745f490&0#{f18a0e88-c30c-11d0-8815-00a0c906bed8}
SymbolicLink \GLOBAL??\USB#ROOT_HUB#4&751fc8a&0#{f18a0e88-c30c-11d0-8815-00a0c906bed8}
SymbolicLink \GLOBAL??\USB#ROOT_HUB20#4&3334158d&0#{f18a0e88-c30c-11d0-8815-00a0c906bed8}
SymbolicLink \GLOBAL??\USB#ROOT_HUB20#4&11a32b3&0#{f18a0e88-c30c-11d0-8815-00a0c906bed8}
SymbolicLink \GLOBAL??\USB#ROOT_HUB30#4&1512d71&0&0#{f18a0e88-c30c-11d0-8815-00a0c906bed8}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{6994ad04-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\PCI#VEN_1022&DEV_7813&SUBSYS_2B56103C&REV_01#3&11583659&0&A7#{79626149-04a0-4353-be16-4b341b1107a9}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{eb115ffc-10c8-4964-831d-6dcb02e6f23f}
SymbolicLink \GLOBAL??\PCI#VEN_10EC&DEV_8179&SUBSYS_804B103C&REV_01#00E04CFFFE81910100#{435b6226-1dcc-43b3-887e-217dbaa27ba3}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{86841137-ed8e-4d97-9975-f2ed56b4430e}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{6994ad04-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{9ff3b516-cd99-4eaf-8373-f2caf87ed26b}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{6994ad04-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{dda54a40-1e4c-11d1-a050-405705c10000}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{6994ad04-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{65e8773e-8f56-11d0-a3b9-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{6994ad04-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\HID#VID_192F&PID_0916#6&2ca5b386&0&0000#{4d1e55b2-f16f-11cf-88cb-001111000030}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{dda54a40-1e4c-11d1-a050-405705c10000}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{6994ad04-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{65e8773d-8f56-11d0-a3b9-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_10EC&DEV_0280&SUBSYS_103C2B56&REV_1000#4&3405719f&0&0001#{eb115ffc-10c8-4964-831d-6dcb02e6f23f}
SymbolicLink \GLOBAL??\HID#VID_04CA&PID_004B&MI_00#7&aa66c92&0&0000#{884b96c3-56ef-11d1-bc8c-00a0c91405dd}
SymbolicLink \GLOBAL??\USB#VID_064E&PID_9324&MI_00#6&17f53ea7&0&0000#{6994ad05-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_1002&DEV_AA01&SUBSYS_00AA0100&REV_1005#4&a0ef172&0&0001#{a17579f0-4fec-4936-9364-249460863be5}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_1002&DEV_AA01&SUBSYS_00AA0100&REV_1005#4&a0ef172&0&0001#{6994ad04-93ef-11d0-a3cc-00a0c9223196}
SymbolicLink \GLOBAL??\HDAUDIO#FUNC_01&VEN_1002&DEV_AA01&SUBSYS_00AA0100&REV_1005#4&a0ef172&0&0001#{dda54a40-1e4c-11d1-a050-405705c10000}
SymbolicLink \GLOBAL??\USB#VID_064E&PID_9324#HF032B-T803-SE01-6-REV0101#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
SymbolicLink \GLOBAL??\USB#VID_192F&PID_0916#5&5788de0&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
SymbolicLink \GLOBAL??\USB#VID_04CA&PID_004B#5&5788de0&0&4#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
SymbolicLink \GLOBAL??\HID#VID_192F&PID_0916#6&2ca5b386&0&0000#{378de44c-56ef-11d1-bc8c-00a0c91405dd}
SymbolicLink \GLOBAL??\HID#VID_04CA&PID_004B&MI_01&Col01#7&889afac&0&0000#{4d1e55b2-f16f-11cf-88cb-001111000030}
SymbolicLink \GLOBAL??\USB#VID_064E&PID_9324&MI_00#6&17f53ea7&0&0000#{e5323777-f976-4f5b-9b55-b94699c46e44}
SymbolicLink \GLOBAL??\USB#VID_064E&PID_9324&MI_00#6&17f53ea7&0&0000#{65e8773d-8f56-11d0-a3b9-00a0c9223196}
SymbolicLink \GLOBAL??\HID#VID_04CA&PID_004B&MI_01&Col02#7&889afac&0&0001#{4d1e55b2-f16f-11cf-88cb-001111000030}
SymbolicLink \GLOBAL??\HID#VID_04CA&PID_004B&MI_01&Col02#7&889afac&0&0001#{4afa3d53-74a7-11d0-be5e-00a0c9062857}
SymbolicLink \GLOBAL??\HID#VID_04CA&PID_004B&MI_00#7&aa66c92&0&0000#{4d1e55b2-f16f-11cf-88cb-001111000030}
SymbolicLink \GLOBAL??\PCI#VEN_1002&DEV_9838&SUBSYS_2B56103C&REV_00#3&11583659&0&08#{5b45201d-f2f2-4f3b-85bb-30ff1f953599}
SymbolicLink \GLOBAL??\PCI#VEN_1002&DEV_9838&SUBSYS_2B56103C&REV_00#3&11583659&0&08#{1ca05180-a699-450a-9a0c-de4fbe3ddd89}
SymbolicLink \GLOBAL??\DISPLAY#HWP424E#4&8e79149&0&UID256#{866519b5-3f07-4c97-b7df-24c5d8a8ccb8}
SymbolicLink \GLOBAL??\ROOT#BasicDisplay#0000#{5b45201d-f2f2-4f3b-85bb-30ff1f953599}
SymbolicLink \GLOBAL??\ROOT#BasicRender#0000#{1ca05180-a699-450a-9a0c-de4fbe3ddd89}
SymbolicLink \GLOBAL??\DISPLAY#HWP424E#4&8e79149&0&UID256#{dbe4373d-3c81-40cb-ace4-e0e5d05f0c9f}
SymbolicLink \GLOBAL??\DISPLAY#HWP424E#4&8e79149&0&UID256#{e6f07b5f-ee97-4a90-b076-33f57bf4eaa7}
SymbolicLink \GLOBAL??\SWD#MMDEVAPI#{0.0.1.00000000}.{3449dc77-9b0f-4ac0-853f-20f6f1439e5b}#{2eef81be-33fa-4800-9670-1cd474972c3f}
SymbolicLink \GLOBAL??\SWD#MMDEVAPI#{0.0.0.00000000}.{faa09b11-fd03-4992-ad57-feafd580ceb7}#{e6327cad-dcec-4949-ae8a-991e976a79d2}
SymbolicLink \GLOBAL??\SWD#MMDEVAPI#MicrosoftGSWavetableSynth#{6dc23320-ab33-4ce4-80d4-bbb3ebbf2814}
SymbolicLink \...\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\Global
SymbolicLink \GLOBAL??\SWD#RADIO#{469B8358-7C69-4CC4-8B82-AF4310768011}#{a8804298-2d5f-42e3-9531-9c8c39eb29ce}
SymbolicLink \GLOBAL??\SWD#IP_TUNNEL_VBUS#ISATAP_1#{ad498944-762f-11d0-8dcb-00c04fc3358c}
SymbolicLink \GLOBAL??\PCI#VEN_10EC&DEV_8179&SUBSYS_804B103C&REV_01#00E04CFFFE81910100#{cac88484-7515-4c03-82e6-71a87abac361}
SymbolicLink \GLOBAL??\PCI#VEN_10EC&DEV_8179&SUBSYS_804B103C&REV_01#00E04CFFFE81910100#{ad498944-762f-11d0-8dcb-00c04fc3358c}
SymbolicLink \GLOBAL??\SWD#IP_TUNNEL_VBUS#ISATAP_1#{cac88484-7515-4c03-82e6-71a87abac361}
SymbolicLink \...\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\Session
SymbolicLink \GLOBAL??\SWD#PRINTENUM#{CE1CC774-39C5-4CBC-A690-0C933B6371A8}#{0ecef634-6ef0-472a-8085-5ad023ecbccd}
SymbolicLink \GLOBAL??\SWD#PRINTENUM#{A0EAEC79-B4F1-47E1-9596-F87656B185C6}#{0ecef634-6ef0-472a-8085-5ad023ecbccd}
SymbolicLink \GLOBAL??\SWD#PRINTENUM#{D943D8D8-F7EB-4400-8EEE-A8CFF8C894B5}#{0ecef634-6ef0-472a-8085-5ad023ecbccd}
SymbolicLink \...\S-1-15-2-930279079-3258969966-1203931420-3379063298-1496040207-3203565093-3038441310\Local
SymbolicLink \GLOBAL??\SWD#PRINTENUM#{FB6B87BC-B5BA-4020-AB9F-E9493D9FB1D5}#{0ecef634-6ef0-472a-8085-5ad023ecbccd}
SymbolicLink \GLOBAL??\SWD#PRINTENUM#{9D7DBACD-D102-4149-B2DB-FFEC94371EAB}#{0ecef634-6ef0-472a-8085-5ad023ecbccd}
SymbolicLink \...\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\Session
SymbolicLink \...\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\Global
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-350187224-1905355452-1037786396-3028148496-2624191407-3283318427-1255436723\Local
SymbolicLink \...\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\Local
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-155514346-2573954481-755741238-1654018636-1233331829-3075935687-2861478708\Session
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\Global
SymbolicLink \...\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\Local
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-95739096-486727260-2033287795-3853587803-1685597119-444378811-2746676523\Global
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\Local
SymbolicLink \...\S-1-15-2-930279079-3258969966-1203931420-3379063298-1496040207-3203565093-3038441310\Session
SymbolicLink \...\S-1-15-2-930279079-3258969966-1203931420-3379063298-1496040207-3203565093-3038441310\Global
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\Global
SymbolicLink \GLOBAL??\SWD#IP_TUNNEL_VBUS#Teredo_Tunnel_Device#{ad498944-762f-11d0-8dcb-00c04fc3358c}
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-1861897761-1695161497-2927542615-642690995-327840285-2659745135-2630312742\Session
SymbolicLink \GLOBAL??\{5d624f94-8850-40c3-a3fa-a4fd2080baf3}#vwifimp_wfd#5&27915378&3&13#{cac88484-7515-4c03-82e6-71a87abac361}
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-95739096-486727260-2033287795-3853587803-1685597119-444378811-2746676523\Session
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-350187224-1905355452-1037786396-3028148496-2624191407-3283318427-1255436723\Global
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-155514346-2573954481-755741238-1654018636-1233331829-3075935687-2861478708\Global
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-350187224-1905355452-1037786396-3028148496-2624191407-3283318427-1255436723\Session
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\Local
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-2551677095-2355568638-4209445997-2436930744-3692183382-387691378-1866284433\Session
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-95739096-486727260-2033287795-3853587803-1685597119-444378811-2746676523\Local
SymbolicLink \GLOBAL??\SWD#IP_TUNNEL_VBUS#Teredo_Tunnel_Device#{cac88484-7515-4c03-82e6-71a87abac361}
SymbolicLink \GLOBAL??\{5d624f94-8850-40c3-a3fa-a4fd2080baf3}#vwifimp_wfd#5&27915378&3&13#{ad498944-762f-11d0-8dcb-00c04fc3358c}
SymbolicLink \Sessions\2\AppContainerNamedObjects\S-1-15-2-155514346-2573954481-755741238-1654018636-1233331829-3075935687-2861478708\Local
Thread System(4): 308
Thread System(4): 616
Thread System(4): 620
Thread System(4): 688
Thread System(4): 1540
Thread System(4): 1848
Thread System(4): 1852
Thread System(4): 1844
Thread System(4): 1988
Thread System(4): 7332
Thread System(4): 2348
Thread System(4): 4340
Thread System(4): 4500
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\NETWORK SERVICE:3e4
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\NETWORK SERVICE:3e4
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\ANONYMOUS LOGON:2abdf
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NARCISMAIN\NiTa:1592015
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\NETWORK SERVICE:3e4
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NARCISMAIN\NiTa:d8945
Token NT AUTHORITY\SYSTEM:3e7
Token NARCISMAIN\NiTa:d8945
Token NARCISMAIN\NiTa:1592015
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NARCISMAIN\NiTa:1592015
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NARCISMAIN\NiTa:1592015
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\SYSTEM:3e7
Token NT AUTHORITY\LOCAL SERVICE:3e5
Token NT AUTHORITY\SYSTEM:3e7

 Posted 23 August 2016 - 03:47 AM
Posted 23 August 2016 - 03:47 AM


 Posted 23 August 2016 - 06:54 AM
Posted 23 August 2016 - 06:54 AM


 Posted 23 August 2016 - 01:09 PM
Posted 23 August 2016 - 01:09 PM


 Posted 24 August 2016 - 10:15 AM
Posted 24 August 2016 - 10:15 AM


 Posted 25 August 2016 - 01:39 AM
Posted 25 August 2016 - 01:39 AM


 Posted 25 August 2016 - 07:09 AM
Posted 25 August 2016 - 07:09 AM


 Posted 26 August 2016 - 03:23 AM
Posted 26 August 2016 - 03:23 AM


 Posted 26 August 2016 - 07:36 AM
Posted 26 August 2016 - 07:36 AM


 Posted 26 August 2016 - 09:41 PM
Posted 26 August 2016 - 09:41 PM

![]()

 Posted 26 August 2016 - 11:21 PM
Posted 26 August 2016 - 11:21 PM


 Posted 28 August 2016 - 05:29 AM
Posted 28 August 2016 - 05:29 AM


 Posted 28 August 2016 - 07:46 AM
Posted 28 August 2016 - 07:46 AM


 Posted 01 September 2016 - 02:06 AM
Posted 01 September 2016 - 02:06 AM


 Posted 01 September 2016 - 06:56 AM
Posted 01 September 2016 - 06:56 AM

















![HP desktop - google.com is in Norwegian [Solved] - last post by wayneman50](https://www.geekstogo.com/forum/uploads/profile/photo-thumb-328601.jpg?_r=1546827512)


 Sign In
Sign In Create Account
Create Account

