What Is It?
By now I’m certain you’ve heard of the Heartbleed bug. If you haven’t, then you should know that it is a flaw found in one of the most common open source SSL implementations on the internet that COULD allow an attacker to get sensitive information from the web server. A successful attack could expose the server’s SSL private keys that would allow the attacker to decrypt the data traveling to the site, such as usernames and passwords.
As of now there have been no confirmed attacks using this bug, but an exploit of the bug is completely untraceable so there’s no way to be certain if a site has been targeted.
Places to learn more:
General information
LastPass and the Heartbleed Bug
How Heartbleed Works: The Code Behind the Internet’s Security Nightmare
How can you tell if a site is affected?
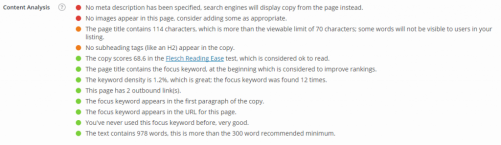
First, you need to figure out how vulnerable your data might be. There are several lists of vulnerable sites that you can manually search through and several online tools that can be used to check specific sites (lastpass and SSL Labs have two particularly useful tools, linked below). There is a Chrome extension that can help identify vulnerable sites as you visit them. The folks at www.Mashable.com have a “hit list” of sorts that lists several sites that they have had direct communication with and recommendations as to what you should do to protect yourself on those sites.
Since Google’s Android operating system is built on open source principles, it is heavily integrated with OpenSSL so any Android device may be vulnerable to this bug as well. Lookout Security has developed a tool to check your device for vulnerability (linked below). If your device is vulnerable you will have to wait for an update for the device.
How can you protect yourself now and in the future?
Once you’ve identified what sites you’ve used that contain sensitive information, you need to change your passwords. You should make sure that they have patched their systems before you change your password for good but many experts are saying that you should change the passwords now just to be sure that any data captured in the last 2 years is safe.
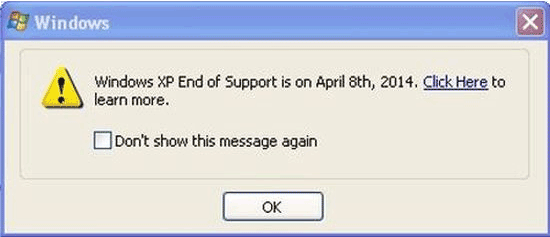
Many systems online were not affected at all because they run on server platforms that don’t use OpenSSL (like Microsoft IIS). These sites have not been compromised by this bug and you should make your own judgment as to whether or not you should change your passwords. If you have used the same username and password combination on an unaffected site as you have on an affected site, you should change your password on both, and make sure they’re different this time.
If you have two factor authentication in place (which you should on any service that supports it) you are at an advantage since even if someone has your username and password they don’t have your second authentication method (typically an app or a text to your mobile phone). You should probably still consider changing your passwords on these sites to be safe.
If you use a password manager (like LastPass or Keepass) then you should most likely regenerate new passwords for your important sites. If you’re using LastPass, they have updated their app to include a tool that will automatically alert you of the Heartbleed status of any sites that you have saved or generated passwords for and give you suggestions as to when you should change their respective passwords.
You should never use the same logon and password for two important sites (like your banking site and your email). If you are using the same information on multiple sites that are important to you, you should change them now so that they are different.
The best thing you can do is not panic and stay aware of the current status of this bug. Keep checking the status of your frequently visited SSL enabled websites and if any of your important sites aren’t patching their systems, find a different company to do business with.

 Xbox All Access offers free hardware up-front, and Game Pass Ultimate for a 2-year subscription price of $24.99 for Series S, or $34.99 for Series X. Game Pass Ultimate includes xCloud streaming, hundreds of Xbox and PC titles, every Microsoft Studio game, and all of EA Play’s titles. After 2 years you own the hardware, for less than if you purchased it and Game Pass Ultimate separately. All-in-all a pretty great deal! Have you checked out
Xbox All Access offers free hardware up-front, and Game Pass Ultimate for a 2-year subscription price of $24.99 for Series S, or $34.99 for Series X. Game Pass Ultimate includes xCloud streaming, hundreds of Xbox and PC titles, every Microsoft Studio game, and all of EA Play’s titles. After 2 years you own the hardware, for less than if you purchased it and Game Pass Ultimate separately. All-in-all a pretty great deal! Have you checked out  I’m guessing the Amazon Flex is probably being returned in large numbers. Which is unfortunate. There’s really nothing wrong with the product, I fact it’s awesome! However, it may not fit the perception of what an Echo device should be.
I’m guessing the Amazon Flex is probably being returned in large numbers. Which is unfortunate. There’s really nothing wrong with the product, I fact it’s awesome! However, it may not fit the perception of what an Echo device should be.